Assessment Brief
Part 1
Learning Outcomes Addressed By This Component:
- Identify where and how simulation can benefit an organisation and its role in design, planning and control of production systems. Including the global environment and a sustainable and ethical global economy.
- Model discrete event data and processes using techniques at the forefront of current best practice to recommend optimized scenarios for a given situation.
Assessment and Submission
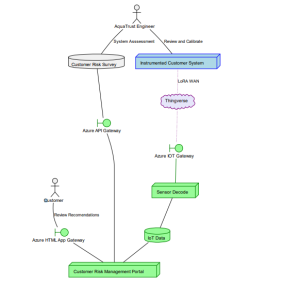
Figure 1: UML Deployment Diagram for the Case Study
Using the UML deployment diagram in Figure 1, and the details of the linked case study, the first part of the assessment looks to model key features of the network. You should use any relevant network simulator for the core of the model, but may use additional tools to model specific features or relevant elements.
The aim of the model should not be a full, low-level, packet simulation. Instead you should concentrate on understanding (and modelling) the relevant packet flows. You may assume on IPv4 only environment, and may use conventional private or documentation ranges (such as the IP ranges do not have to be ‘realistic’). However where there are conversions between public and private IP ranges, you should take these into account and note the impact the conversions have.
Similarly, devices in the network do not have to be fully modelled. For instance the ‘IOT Gateway’ does not require a full application-level simulation, including OS models and the full details of Layer 1 modelling. However your model should be able to simulate relevant aspects of the IOT Gateway, for instance details relevant to the chosen Layer 3/4 transport, or the Layer 7 protocol used.
Do You Need Assignment of This Question
You should then summarise the conclusions you draw from your model in a report of approximately 2,000 words. You should include at least the following secions, but you may vary the content and detail and required
- Introduction. A brief summary of the technical solutions and other relevant work related to the design that you will present. You do not have to include the full case study: only include relevant features. This introduction should include a variety of sources drawn from the academic literature which supports and develops the design and techniques you are creating.
- Proposal. Articulate the design, using relevant technical drawing and documentation, external evidence and other relevant factors. Again, this is not the complete network design: focus on the area you your models covers. However you should incorporate a justification for your design which covers the key interactions of the two main actors (Aquatrust Engineer and Customer) in the three main use cases
- The Customer reviewing the analysis and recommendations held in the Customer Risk Management Portal from their own device and on their own network
- An Aquatrust Engineer using a company device to update company records remotely over the public Internet
- The Instrumented Customer System sending sensor data over a public LoRa WAN connection to the Azure IOT Gateway for processing (Sensor Decode) and storage (IoT Data)
Feedback
Your assessment will be marked across three criteria, and feedback will be given on each to help you improve your work in the future. Below we have outlined the five are we will be assessing, together with both the general skills we are focusing on and how these skills are expected to be translated for Engineering Simulation. We have also then given two indicative grade bands
Information Collection. Your ability to find and select appropriate methods, tools, and techniques from the research literature that relate to the problem you have chosen. For Engineering Simulation, we are particularly looking at your ability to use this research literature critically selecting (and presenting) sources that build your own arguments; and your ability to evaluate the selection of sources that help you to synthesise your own arguments for the reader.
1st Class: Demonstrates a very good, comprehensive approach and engagement with the critical use of appropriate methods and research tools from the academic literature. Sources for evidence and arguments from the literature are clearly provided; and the presentation and analysis of the sources are well presented. Very good consistent evidence of independent thought or reasoning throughout.
Pass: Demonstrates a satisfactory understanding and engagement with appropriate academic literature; and the sources for the methods and tools drawn from the literature. All sources of original evidence are acknowledged, and the presentation and analysis of those sources are appropriately presented. Shows some independent thought but may have some omissions.
Technical Capabilities. Your ability to understand the technical research literature, and use that literature to provide appropriate solutions to the sustainability problem that you have chosen to focus on. For this assessment we are looking closely at the evidence base you choose to use; this could be chosen solely from the literature, or it could include a limited model or other technical artefact to help you to develop your own arguments. Whatever evidence base you choose to use, the technical solutions (and the limitations or assumptions) of that solution should be clearly evident to the reader.
1st Class: Very good selection and consistent effective application of a range of appropriate tools and techniques applied to novel situations to achieve innovative solutions.
Pass: Demonstrates an appropriate selection and application of tools and techniques. Tool use and application may need some development at times to achieve solutions.
Buy Answer of This Assessment & Raise Your Grades
Communication. Your ability to convey the arguments you are making in a succinct, clear, and consistent manner. In this assessment we are especially focusing on your ability to synthesise the arguments of other researchers, and to convey those discussions in your own words to build a clear argument for the reader.
1st Class: Engaging and accomplished. Very high-quality, fluent academic writing style with accurate spelling and syntax. All thoughts and ideas expressed clearly. Appropriate, accurately cited, and complete references from a comprehensive range of sources
Pass: Satisfactory quality of academic expression, meaning, and clarity demonstrated with only minor areas identified for improvement. Appropriate, accurately cited, and complete references from a limited range of sources.
Part 2
Learning Outcomes Addressed By This Component:
- Identify where and how simulation can benefit an organisation and its role in design, planning and control of production systems. Including the global environment and a sustainable and ethical global economy.
- Critically analyse real world data to offer alternative solutions, including a financial rationale for change, based on the predicted results from the discrete element simulator.
Assessment and Submission
For the second part of the Engineering Simulation module, you should reflect on your model from Part 1, and highlight the key security recommendations. Whilst you should base your on a technical understanding, you should assume the audience of the report is not from this background. Think about how you would present your findings to members of the company board, for example.
You may expand the scope of your conclusions, but you are expected to cover at least the three key use cases from Part 1
- The Customer reviewing the analysis and recommendations held in the Customer Risk Management Portal from their own device and on their own network
- An Aquatrust Engineer using a company device to update company records remotely over the public Internet
- The Instrumented Customer System sending sensor data over a public LoRa WAN connection to the Azure IOT Gateway for processing (Sensor Decode) and storage (IoT Data)
You should be creative in the way you show the data and underlying evidence base. For example, detailed packet traces are unlikely to be helpful. But the impact of protocol issues presented as an infographic in a way the business can understand (loss of customer data, impact on reputation, etc.) is much more useful. Look at the way the popular and business press have reported recent security incidents for guidance.
The final report should be a maximum of 2,000 words, excluding images. All references should be in the University standard format.
Feedback
Your assessment will be marked across three criteria, and feedback will be given on each to help you improve your work in the future. Below we have outlined the five are we will be assessing, together with both the general skills we are focusing on and how these skills are expected to be translated for Engineering Simulation. We have also then given two indicative grade bands
Pass. This is the minimum we would expect in each criteria, and would indicate an assessment with an overall mark between 50% and 59%.
1st Class. A very good attempt in the relevant criteria which satisfies everything we are looking for. Consistent work in this area would indicate and overall mark between 70% and 85%.
When we give you feedback, we will seek to focus on giving you feedback that will improve your work in the future. In other words we will focus our feedback for the assessment on looking forward and not looking back. We would, though, be happy to discuss your work in detail individually and where the strengths and weaknesses of your work are with relation to the specific assessment set.
However the overall mark will be based on consistently achieving the standard we ask for in each of the five criteria below. For instance a distinction level mark (above 70%) in one area will not necessarily result in a distinction overall. Instead we are looking for a balance across all the skills we are looking at below, and your mark will reflect our judgement of how consistently you are meeting the following criteria
Communication. Your ability to convey the arguments you are making in a succinct, clear, and consistent manner. In this assessment we are especially focusing on your ability to synthesise the arguments of other researchers, and to convey those discussions in your own words to build a clear argument for the reader.
1st Class: Engaging and accomplished. Very high-quality, fluent academic writing style with accurate spelling and syntax. All thoughts and ideas expressed clearly. Appropriate, accurately cited, and complete references from a comprehensive range of sources
Pass: Satisfactory quality of academic expression, meaning, and clarity demonstrated with only minor areas identified for improvement. Appropriate, accurately cited, and complete references from a limited range of sources.
Are You Looking for Answer of This Assignment or Essay
Synthesis and Evaluation. Your ability to connect ideas together to develop well-reasoned arguments, using the literature to consistently underpin those arguments with a range of well-defined source from multiple viewpoints. For many sources in the area of sustainability the evidence and arguments will come with significant limitations: and in some case will be contradictory or offer poorly understood effects. A good argument should understand the limitations of the evidence being presented in individual sources, and be able to either combine multiple sources to offer an effective foundation for the argument: or to work within the limitations of the sources being used in the conclusions drawn from that evidence base.
1st Class: Very good demonstration of independent thought, new connections between ideas and critical, well-reasoned engagement with a range of consistently, well justified alternative views.
Pass: Contains some independent thinking and justification. There may be some development required in the combining of ideas and critically engaging with the evaluation of alternative views from alternative sources.
Reflection. Your ability to consider the issues surrounding your chosen problem from a range of viewpoints (sometimes contradictory ones). Solutions offered to improve sustainability are only very rarely ‘obvious’ or without caveats or limitations. For instance certain techniques for processing may have impact on the water sources in that community; or moving production to reduce the ecosystem impact may then affect the social or economic structure of the host community. Here we are looking for your ability to understand the issues that you raise from a diverse range of viewpoints, and clearly articulate the limitations of your solution and the potential range of impacts it might have.
1st Class: Very good, evidence demonstrated indicating full responsibility for your own learning, and the capacity to advance your knowledge and develop new skills to a high level. Very good, effective use of structure in the reflection to show the range of viewpoints considered. A clear, consistent use of evidence throughout the reflective process, with the outcomes articulated in some detail in terms how they impact on issues related to the presented solution.
Pass: Adequate evidence of a commitment to advance personal knowledge and develop skills. Some evidence that the chosen solutions has been critically deliberated on and considered from different perspectives/ settings. Some development required on citing evidence that the process and outcomes related to the solution have been considered.
The post Simulation and Security Analysis of IoT-Integrated Risk Management Networks: A Case Study of Aquatrust Systems – Semester B Level 6 appeared first on Students Assignment Help UK.